 07-21-2010, 09:12 AM
07-21-2010, 09:12 AM
|
#1
|
|
Franchise Player
Join Date: Aug 2005
Location: Calgary
|
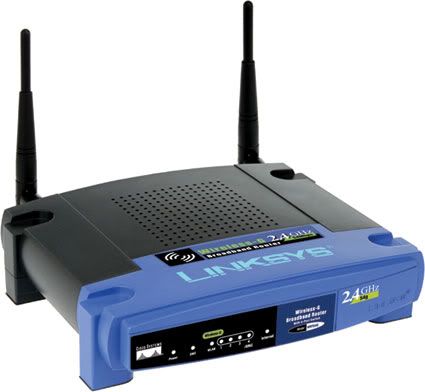
 Anyone have a Linksys Router?
Anyone have a Linksys Router?
News is sketchy at best, but apparently a security researcher at the Black Hat Conference in 7 days will release a "DNS Rebuilding" exploit for Linksys Routers with the default and different flavours of Linux Firmware (not sure if my tomato firmware is exploitable). Not sure if the hack only works on the default or simple passwords or anything (my "secure" password I use for alot of things is 19 characters long with 3 special characters, 4 capital letters, 9 numbers).
http://www.engadget.com/2010/07/21/r...s-of-home-rou/
I might be buying a few DLinks today because of this.
http://accessories.dell.com/sna/prod...1&sku=A3455167
__________________
MYK - Supports Arizona to democtratically pass laws for the state of Arizona
Rudy was the only hope in 08
2011 Election: Cons 40% - Nanos 38% Ekos 34%
Last edited by mykalberta; 07-21-2010 at 09:20 AM.
|

|

|
 07-21-2010, 09:30 AM
07-21-2010, 09:30 AM
|
#2
|
|
#1 Goaltender
|
Quote:
Originally Posted by mykalberta

(my "secure" password I use for alot of things is 19 characters long with 3 special characters, 4 capital letters, 9 numbers).
|
HAHAHAHA then its not very secure at all is it...its being used multiple times.
__________________
-Scott
|

|

|
 07-21-2010, 09:33 AM
07-21-2010, 09:33 AM
|
#3
|
|
#1 Goaltender
|
One a serious note, this exploit is not as bad as it sounds - it tricks the router into exposing the administration page because the router thinks the requester is on the internal network, when in fact they are external. From there, they still need to guess the password to the admin page.
Which is easier, of course, when your “secure” 19 character long password, is in play at multiple sites.
__________________
-Scott
|

|

|
 07-21-2010, 09:44 AM
07-21-2010, 09:44 AM
|
#4
|
|
Playboy Mansion Poolboy
Join Date: Apr 2004
Location: Close enough to make a beer run during a TV timeout
|
Quote:
Originally Posted by mykalberta

I might be buying a few DLinks today because of this.
|
I was going to start a new thread on this, but I think the current batch of Dlinks are flawed. I don't have the model numbers handy, but it looks like 4 out of the 4 I have for myself and friends have issues. Dropping signals, not allowing machines to connect, etc.
|

|

|
 07-21-2010, 09:50 AM
07-21-2010, 09:50 AM
|
#5
|
|
Franchise Player
Join Date: Aug 2005
Location: Calgary
|
Quote:
Originally Posted by sclitheroe

HAHAHAHA then its not very secure at all is it...its being used multiple times.
|
If they crack it they crack it. One great password is better than 5 ok passwords imo - not all of us use calgaryflames001, 002, 003, 004 as our passwords.
__________________
MYK - Supports Arizona to democtratically pass laws for the state of Arizona
Rudy was the only hope in 08
2011 Election: Cons 40% - Nanos 38% Ekos 34%
|

|

|
 07-21-2010, 09:51 AM
07-21-2010, 09:51 AM
|
#6
|
|
Franchise Player
Join Date: Aug 2005
Location: Calgary
|
Quote:
Originally Posted by ken0042

I was going to start a new thread on this, but I think the current batch of Dlinks are flawed. I don't have the model numbers handy, but it looks like 4 out of the 4 I have for myself and friends have issues. Dropping signals, not allowing machines to connect, etc.
|
The one I linked to has fairly good reviews on newegg but normally I would agree, DLink blows.
__________________
MYK - Supports Arizona to democtratically pass laws for the state of Arizona
Rudy was the only hope in 08
2011 Election: Cons 40% - Nanos 38% Ekos 34%
|

|

|
 07-21-2010, 10:42 AM
07-21-2010, 10:42 AM
|
#7
|
|
#1 Goaltender
|
The DNS rebinding bug is not a good enough reason to replace a router, in my opinion. Changing the default admin page password will reduce them to having to attempt a brute-force crack. That’s not low hanging fruit that can be easily exploited.
__________________
-Scott
|

|

|
 07-21-2010, 11:32 AM
07-21-2010, 11:32 AM
|
#8
|
|
Franchise Player
Join Date: Nov 2006
Location: Supporting Urban Sprawl
|
Quote:
Originally Posted by mykalberta

If they crack it they crack it. One great password is better than 5 ok passwords imo - not all of us use calgaryflames001, 002, 003, 004 as our passwords.
|
It is not about cracking the password itself, it is about finding a place you use it that doesn't have as good of security as it should.
Imagine this, you sign up for www.bobshouseofabortionphotos.com and use your superpassword. Next month, some anti-abortion nutjob hacks into the system and somehow retrieves all the password information because Bob didn't think it was important to have the passwords encrypted because it really slowed down log in on his Dell PowerEdge 110T server in his basement. Now someone not only has a list of IP addresses of those people who access that site, but he has a list of passwords that they use.
__________________
"Wake up, Luigi! The only time plumbers sleep on the job is when we're working by the hour."
|

|

|
 07-22-2010, 06:01 PM
07-22-2010, 06:01 PM
|
#9
|
|
Threadkiller
Join Date: Oct 2003
Location: 51.0544° N, 114.0669° W
|
|

|

|
 07-28-2010, 08:55 PM
07-28-2010, 08:55 PM
|
#11
|
|
First Line Centre
|
Quote:
Originally Posted by Rathji

It is not about cracking the password itself, it is about finding a place you use it that doesn't have as good of security as it should.
Imagine this, you sign up for www.bobshouseofabortionphotos.com and use your superpassword. Next month, some anti-abortion nutjob hacks into the system and somehow retrieves all the password information because Bob didn't think it was important to have the passwords encrypted because it really slowed down log in on his Dell PowerEdge 110T server in his basement. Now someone not only has a list of IP addresses of those people who access that site, but he has a list of passwords that they use. |
FYI - that's not a real site. Just checked.
...just in case any of your were curious...
|

|

|
|
The Following 2 Users Say Thank You to Phaneuf3 For This Useful Post:
|
|
 Posting Rules
Posting Rules
|
You may not post new threads
You may not post replies
You may not post attachments
You may not edit your posts
HTML code is Off
|
|
|
All times are GMT -6. The time now is 09:00 PM.
|
|

